How Face Authentication Works in Government Services
In recent years, governments around the world have rapidly embraced digital transformation to improve service delivery, enhance security, and reduce fraud. One of the most impactful technologies driving this transformation is face authentication, a form of biometric verification that uses an individual’s facial features to confirm their identity.
From accessing welfare schemes and pensions to verifying identity for digital documents, face authentication is becoming an essential component of modern governance. In countries like India, initiatives such as Aadhaar-based authentication and mobile face verification apps have already begun reshaping how citizens interact with government systems.
This article explores how face authentication works, its underlying technology, its applications in government services, benefits, challenges, and the future of this powerful tool.
What is face authentication?
Face authentication is a biometric security process that identifies or verifies a person using their facial features. Unlike traditional methods such as passwords, PINs, or ID cards, facial authentication relies on unique biological characteristics that are difficult to replicate.
There are two key processes involved:
- Face Detection: Identifying a face within an image or video frame.
- Face Recognition Authentication: Matching the detected face against a stored database to confirm identity.
Government systems typically use face authentication for verification (1:1 matching) rather than identification (1:N matching), meaning the system checks if a person is who they claim to be.

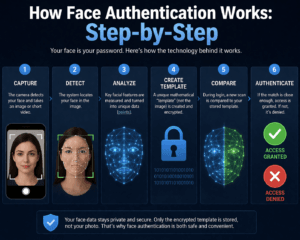
How Face Authentication Works: Step-by-Step
1. Image Capture
The process begins with capturing an image or live video of the user through a device such as
- Smartphone camera
- Webcam
- Kiosk camera at service centers
In government services, users often capture a live selfie through official apps or portals.
2. Face Detection
The system scans the image to detect the presence of a face. Advanced algorithms identify key facial landmarks such as
- Eyes
- Nose
- Mouth
- Jawline
This ensures that the image contains a valid human face and not an object or background.
3. Feature Extraction
Once the face is detected, the system analyzes and converts it into a mathematical representation known as a face template or faceprint.
Key features analyzed include:
- Distance between eyes
- Shape of cheekbones
- Contour of lips
- Facial symmetry
Modern systems use deep learning models (like convolutional neural networks) to extract highly accurate features.
4. Liveness Detection
To prevent fraud (such as using photos or videos), systems perform liveness checks. These may include:
- Asking the user to blink or smile
- Detecting natural facial movements
- Checking depth and lighting variations
This step ensures that the person is physically present and not spoofing the system.
5. Matching with Database
The extracted face template is compared against stored records in a secure government database.
- 1:1 Matching: Comparing with a specific record (e.g., Aadhaar number)
- 1:N Matching: Searching across multiple records (used less often due to privacy concerns)
If the match score crosses a predefined threshold, authentication is successful.
6. Decision and Access Grant
Based on the match result:
- Access is granted (e.g., approval of service, login, benefit transfer)
- Or access is denied (if mismatch occurs)
The entire process typically takes a few seconds, making it highly efficient.
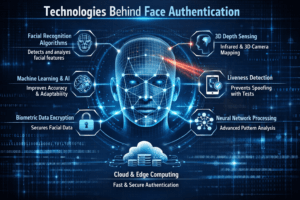
Technologies Behind Face Authentication
Face authentication relies on a combination of advanced technologies:
1. Artificial Intelligence (AI)
AI models analyze facial patterns and improve accuracy over time. Machine learning allows systems to adapt to
- Aging
- Lighting changes
- Minor facial changes
2. Deep Learning
Deep neural networks (especially CNNs) enable high-precision feature extraction and matching. These models are trained on large datasets to recognize millions of facial variations.
3. Computer Vision
Computer vision helps systems interpret and process visual data from images and videos.
4. Cloud Computing
Government systems often use cloud infrastructure to:
- Store biometric data securely
- Perform large-scale matching
- Enable real-time authentication
5. Encryption and Security Protocols
Biometric data is encrypted to protect user privacy. Governments implement:
- End-to-end encryption
- Secure APIs
- Data protection policies
Applications in Government Services
Face authentication is being used across a wide range of government functions:
1. Digital Identity Verification
In India, Aadhaar-based face authentication allows citizens to verify identity without fingerprints or OTPs.
2. Welfare and Subsidy Distribution
Face authentication helps ensure that benefits reach the rightful beneficiaries by eliminating:
- Duplicate identities
- Ghost beneficiaries
3. Pension Verification
Elderly citizens can verify their identity remotely using face authentication instead of visiting offices physically.
4. e-Governance Portals
Users can log in securely to government portals using facial recognition instead of passwords.
5. Law Enforcement and Security
Authorities use face recognition systems for:
- Criminal identification
- Surveillance
- Missing person tracking
6. Immigration and Border Control
Airports use facial authentication for:
- Automated check-ins
- Passport verification
- Faster immigration clearance
7. Attendance Systems
Government offices and schools use face-based attendance systems to improve transparency.

Benefits of Face Authentication in Government Services
1. Enhanced Security
Facial features are unique and difficult to forge, reducing identity fraud.
2. Convenience for Citizens
No need to remember passwords or carry ID cards. Authentication can be done:
- Anytime
- Anywhere
3. Faster Service Delivery
Face authentication reduces processing time, enabling quicker access to services.
4. Reduced Fraud and Leakages
Helps eliminate fake beneficiaries in welfare schemes, saving public funds.
5. Contactless Verification
Especially useful during pandemics or in remote areas where physical interaction is limited.
6. Inclusivity
People who face difficulties with fingerprints (e.g., the elderly, manual laborers) can use face authentication easily.

Challenges and Concerns
Despite its advantages, face authentication raises several concerns:
1. Privacy Issues
Storing biometric data can lead to misuse if not properly protected.
2. Data Security Risks
Government databases are attractive targets for cyberattacks.
3. Accuracy and Bias
Some systems may show reduced accuracy for:
- Different skin tones
- Age groups
- Lighting conditions
4. Infrastructure Limitations
Rural areas may face challenges due to
- Poor internet connectivity
- Lack of devices
5. Legal and Ethical Concerns
Questions arise about:
- Consent
- Data ownership
- Surveillance misuse
Measures to Ensure Safe Implementation
Governments are taking steps to address these challenges:
1. Strong Data Protection Laws
Implementing regulations to safeguard biometric data.
2. Consent-Based Authentication
Ensuring users approve the use of their facial data.
3. Regular Audits and Testing
Improving system accuracy and eliminating bias.
4. Decentralized Storage
Reducing risks by avoiding centralized data storage.
5. Public Awareness
Educating citizens about how their data is used and protected.

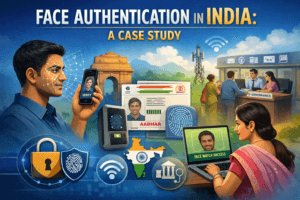
Face Authentication in India: A Case Study
India has been a pioneer in biometric authentication through the Aadhaar system.
Recent developments include:
- Aadhaar Face Authentication App
- Integration with DigiLocker
- Use in pension and ration distribution
The system allows users to authenticate identity using just a smartphone, making services more accessible.
Future of Face Authentication in Government Services
The future of face authentication looks promising with advancements such as
1. 3D Face Recognition
Improved accuracy using depth sensing technologies.
2. AI-Powered Anti-Spoofing
More advanced liveness detection to prevent fraud.
3. Integration with Digital IDs
Seamless access to multiple services through a single identity system.
4. Edge Computing
Faster processing directly on devices without relying heavily on cloud servers.
5. Global Adoption
More countries are expected to adopt face authentication for digital governance.

Conclusion
Face authentication is transforming the way governments deliver services by making them more secure, efficient, and accessible. By leveraging advanced technologies such as AI and biometrics, governments can ensure that services reach the right individuals while reducing fraud and administrative burdens.
However, the success of this technology depends on balancing innovation with privacy, security, and ethical considerations. With proper safeguards and transparent policies, face authentication has the potential to revolutionize governance and create a more inclusive digital future.
1 thought on “How Face Authentication Works in Government Services”